User Notice: Action required as part of upcoming Compute Canada security improvements
To enhance the security of its resources, Compute Canada is modifying the configuration of the SSH security protocol used to connect to its clusters. SSH protects the information transmitted between the user and the cluster, and verifies the identity of both parties.
The new configuration will affect all users and requires action from you. For details on the upcoming changes, see our wiki page: https://docs.computecanada.ca/wiki/SSH_security_improvements.
Implementation date
The changes will be implemented a few weeks from now; you will be notified by email 10 days prior to the actual date. Users who haven’t completed the process described below will be unable to connect to Béluga, Cedar, Graham and Niagara.
Action required
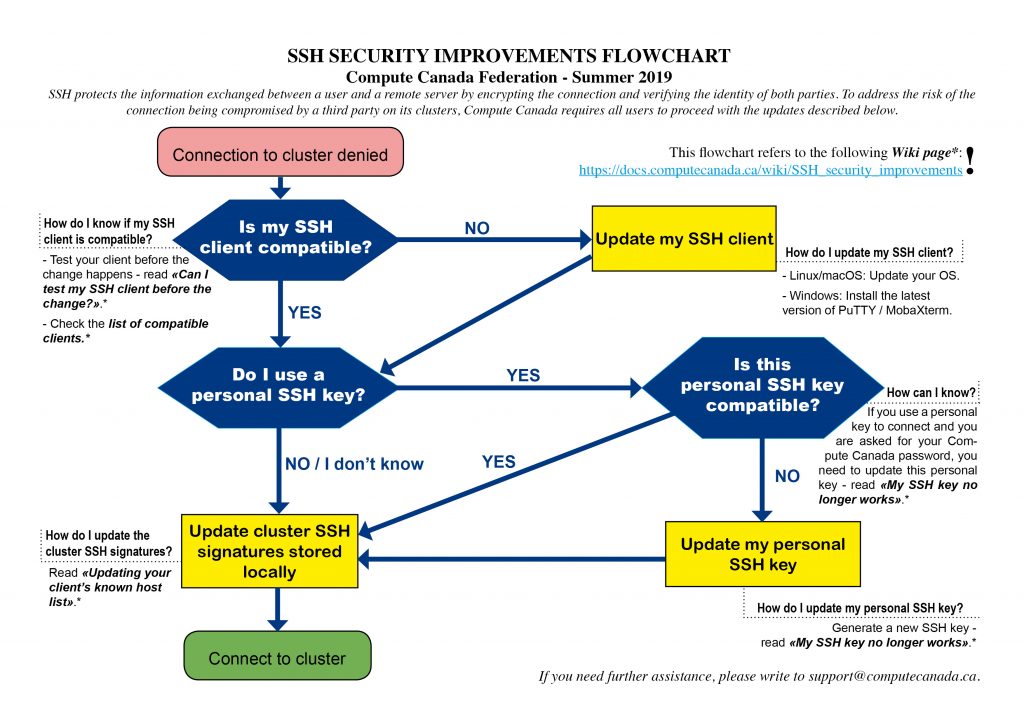
This flowchart describes the steps you need to take:
Prior to implementation, test your SSH client by connecting to server ssh-test.computecanada.ca using your Compute Canada credentials.
- If you can’t connect, update your SSH client.
- If you can connect, your SSH client is compatible and no further action is required until the implementation date (see next step below).
Following implementation, all users have to update the local copies of the host key, which is used to identify each Compute Canada cluster.
Note: If you use a personal SSH key, you may also have to generate a new key pair. To find out in advance, you can try to use your personal key on the
ssh-test.computecanada.ca test server.
Need help?
If you require further assistance, please email support@computecanada.ca.